M365Lyon Kit Reparación Cable Luz Trasera Patinete Eléctrico Xiaomi M365 y M365 Pro : Amazon.es: Deportes y aire libre

Accesorio patinete eléctrico - SK8 Luz trasera, Para Xiaomi Mi Electric Scooter M365 y Pro, Negro | MediaMarkt

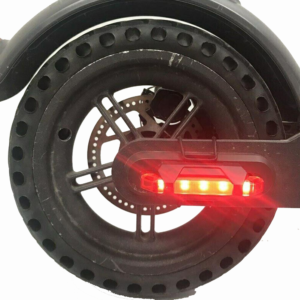
myBESTscooter - Luz trasera led de repuesto de la lámpara para Xiaomi 1S Essential Pro2 Mi3 Patinete eléctrico : Amazon.es: Deportes y aire libre
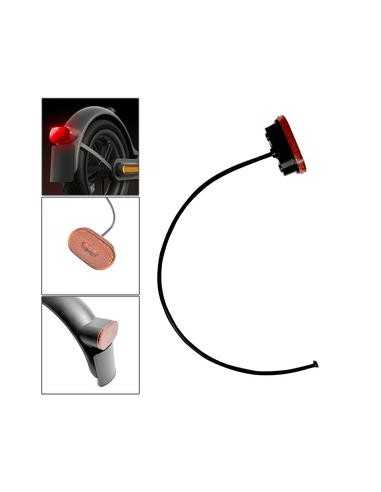
![M365Lyon] - Cable de luz trasera reforzado conector de batería freno en el guardabarros para patinete eléctrico Xiaomi M365 Pro2 Essential Pro 1S : Amazon.es: Deportes y aire libre M365Lyon] - Cable de luz trasera reforzado conector de batería freno en el guardabarros para patinete eléctrico Xiaomi M365 Pro2 Essential Pro 1S : Amazon.es: Deportes y aire libre](https://m.media-amazon.com/images/I/61WvEsTLAkS._AC_UF1000,1000_QL80_.jpg)