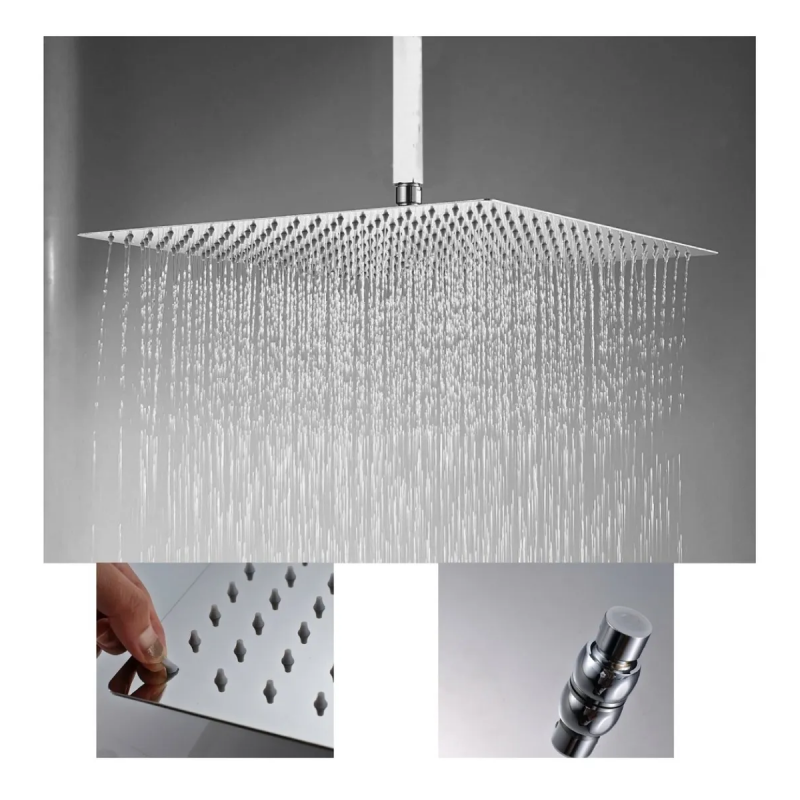
Regaderas para Baño 12 Pulgadas Con Brazos de Ducha de 40 cm, TXG Cabeza de Ducha de Lluvia de Alta Presión, Regadera Cuadrada De Acero Inoxidable (12 Pulgadas) : Amazon.com.mx: Herramientas y

Cabezal de Ducha Regadera Tipo Lluvia Cascada de Acero Mate Picool Regadera Tipo Lluvia | Walmart en línea

Estos son los cinco tipos de regaderas para baños número uno en ventas | Escaparate | EL PAÍS México

PICOOL Regaderas para baño Cuadrada Tipo Lluvia Cromada incluye tubo 40 cm alta presion,montaje fijo de cabeza de ducha 20cm,conector de rotacion de 360 grados,regaderas fija baño : Amazon.com.mx: Herramientas y Mejoras

TEKXDD Sistema de Ducha de Lluvia - Regadera Negra, Juego de Mezclador de Ducha de Techo para Baño, Cabezal de Ducha de Lluvia de Alta Presión con Combinación de Válvula de Mezcla